NIST weighs in on the blockchain
I stumbled on this somewhat interesting document this morning: earlier this month, the National Institute of Standards and Technology (NIST), published NISTIR 8202, Blockchain Technology Overview. It’s a relatively long and thorough overview of the basic technology supporting different types of blockchains, from cryptographic hashes, private and public keys, all the way to different consensus models, and smart contracts. However, as the document states in the introduction, it is not a technical guide.
If you don’t know much about how blockchain works but are kind of interested, it’s a useful read. I’d also recommend checking out my overview on blockchain if you’re interested in a bit more of a technical treatment.
One of the more amusing parts of the paper is Figure 6 from page 42:
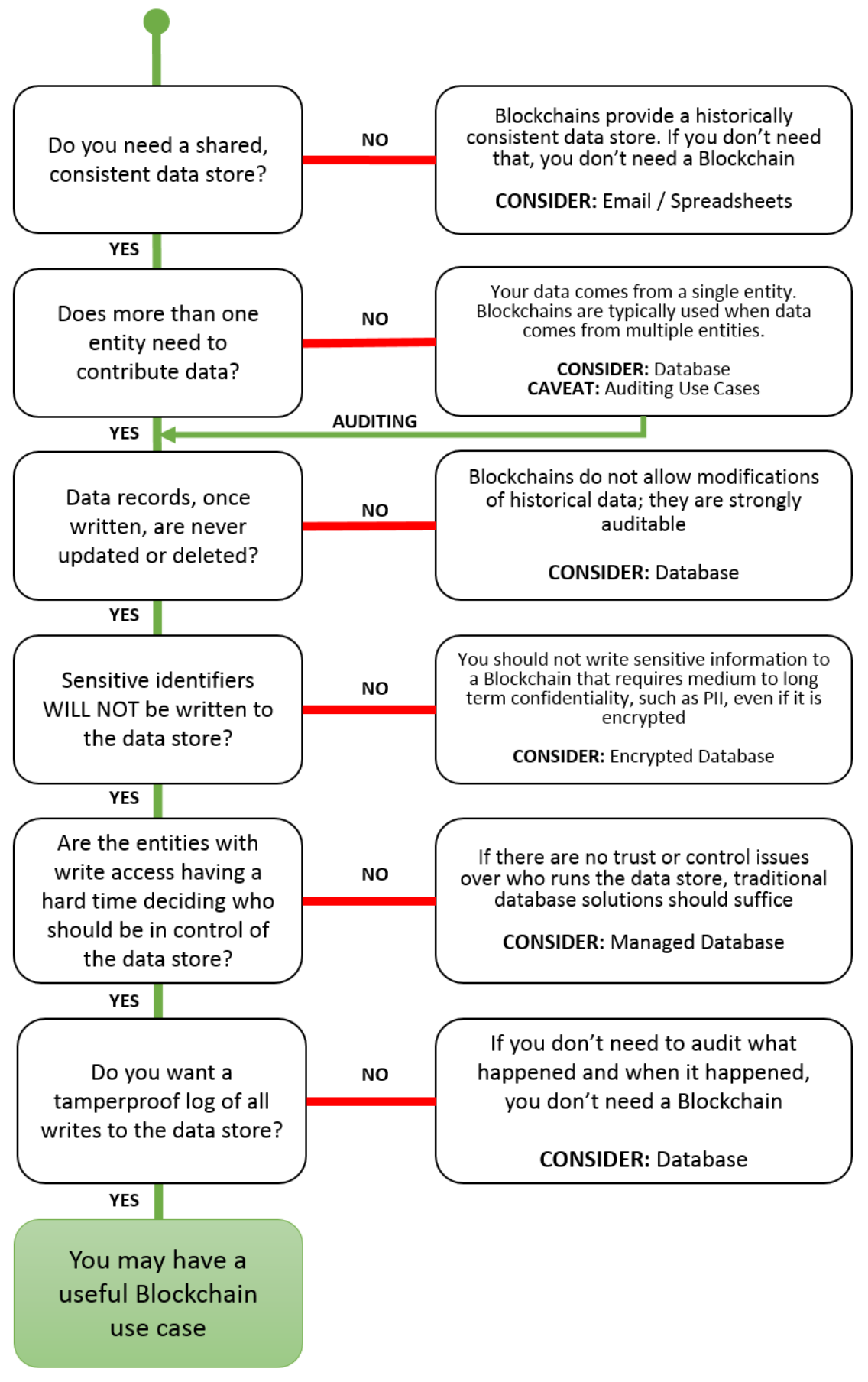
Let me summarise it for you: you may have a useful Blockchain use case if: you need a shared, consistent data store; where more than one entity needs to contribute data; and that data, once written is never updated or deleted; and it’s also not sensitive nor contains any sensitive identifiers; and there’s trust or control issues over who should be in control of the data; and you want the datastore to be a tamperproof log of all writes. In all other cases, the NIST recommends using a database, possibly managed or encrypted; or then just email and spreasheets.
Update: Seems Bruce MacDonald from GitHub also found this amusing; and made this little interactive questionaire.
